Launch App
Try the full experience right now — zero setup.
Integration Quickstart
Run your first integration loop in minutes.
Explore the Product
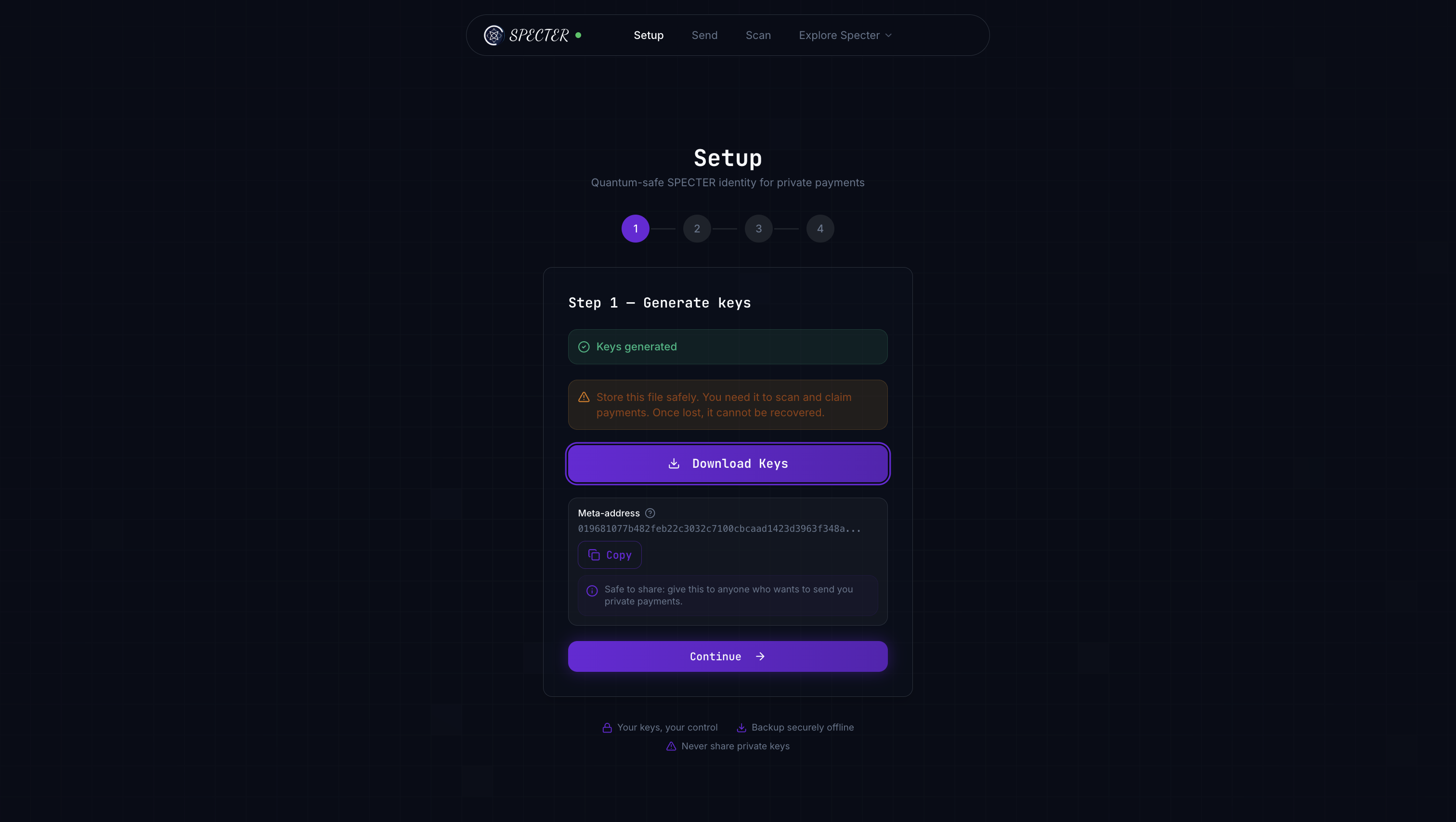
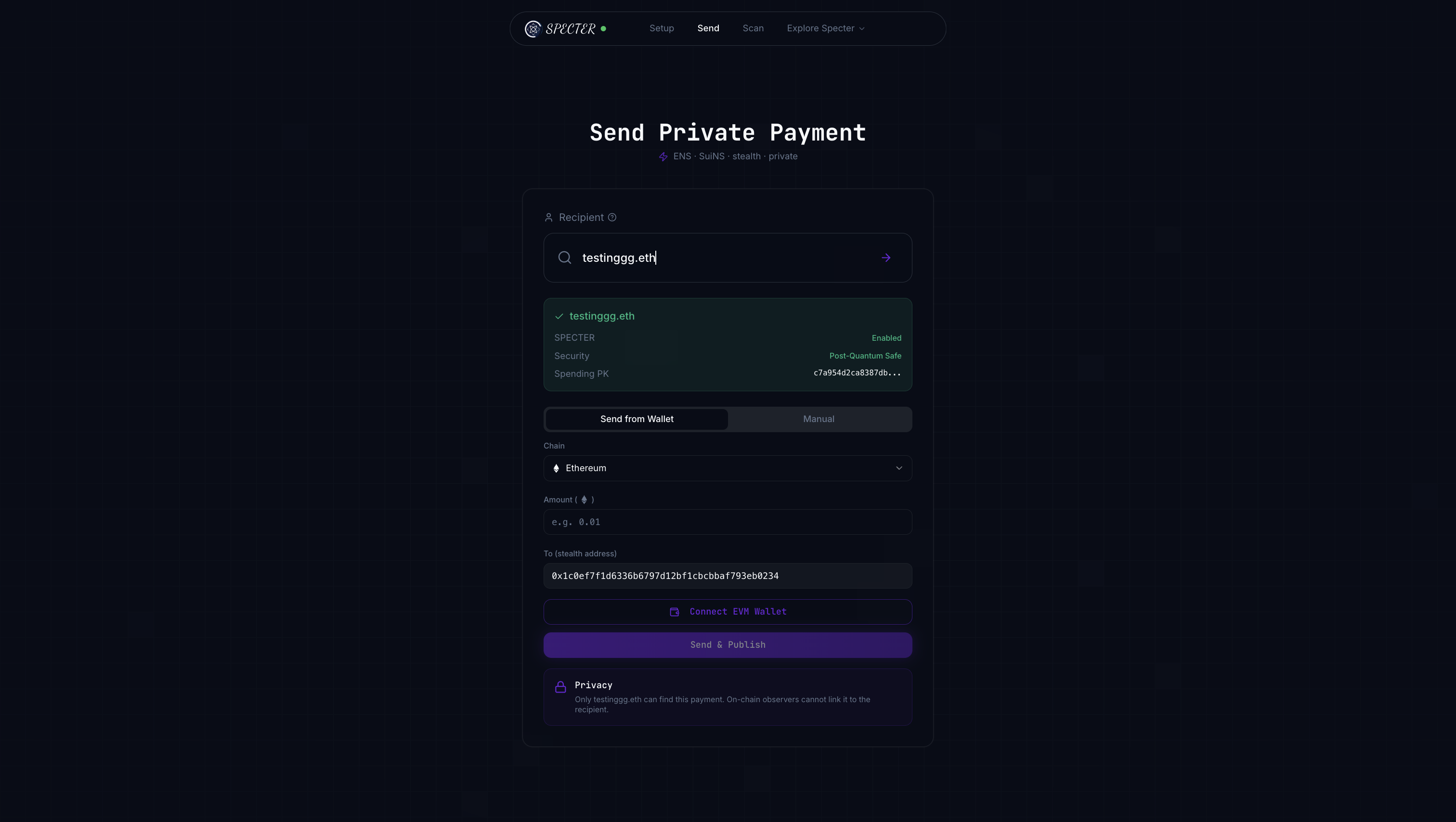
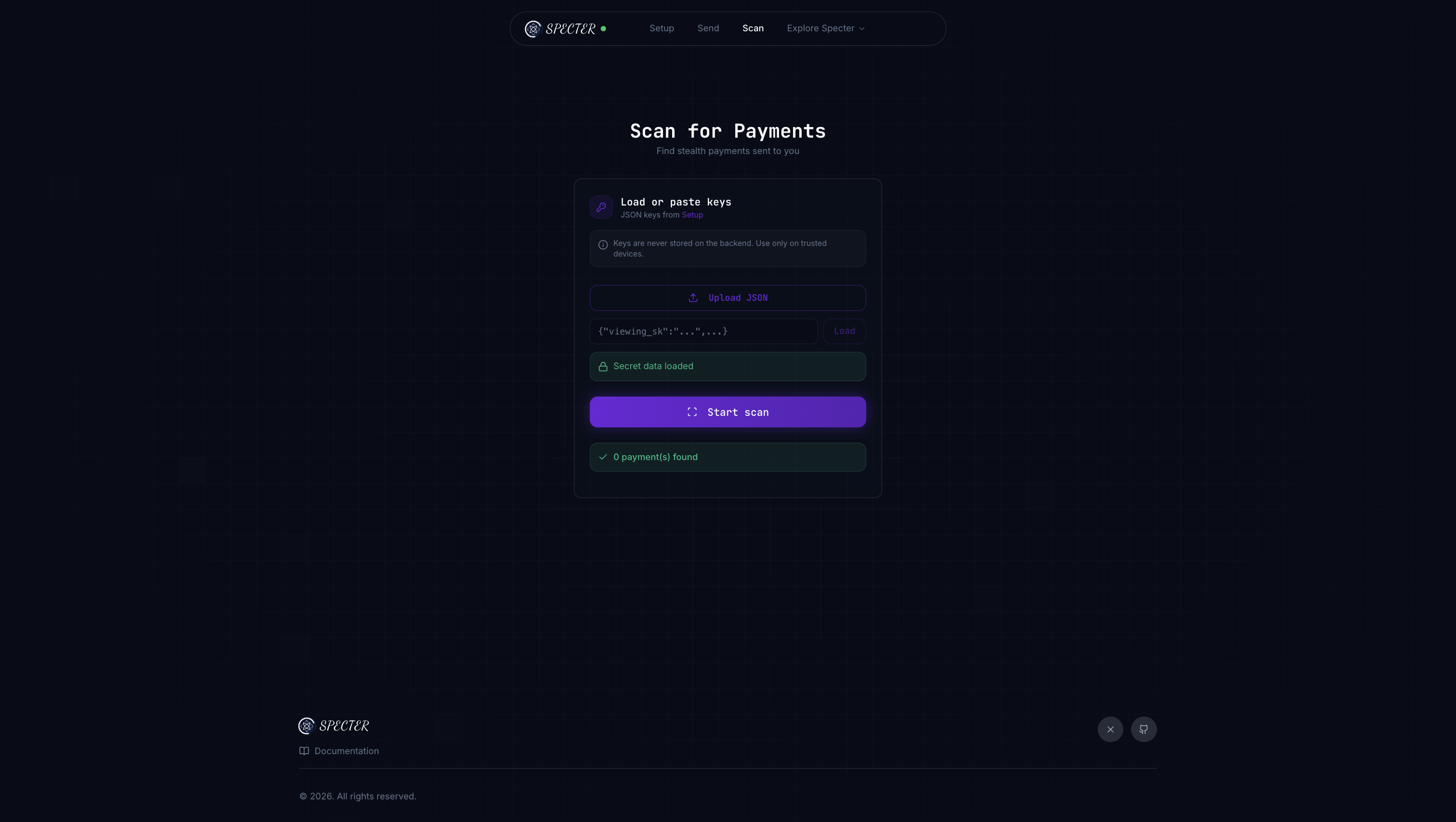
Take a visual tour of what users see.
The Problem We Solve
Every blockchain transaction is public. When someone sends you money, anyone can trace that payment back to your identity, see your balance, and track your activity. SPECTER makes payments private. It gives every recipient a way to receive funds at unique, one-time addresses that cannot be linked back to their main wallet — even by someone watching every transaction on the chain. And it does this with post-quantum cryptography (ML-KEM-768), meaning your privacy stays safe even when quantum computers arrive.The Analogy — Think “Secure Mail Concierge”
Imagine you live in an apartment building:You share your building address
You give out your building’s public address — anyone can send you packages. This is your meta-address (public profile).
Every package goes to a fresh locker
Instead of delivering to your door, each package gets its own brand-new private locker. This is the stealth address — unique for every payment.
A delivery notice is posted
The concierge posts a coded notice on the board. This is the announcement — it’s public, but only you can decode which locker is yours.
How It Works — The 4-Step Flow
| Step | What happens | Who does it |
|---|---|---|
| 1. Profile | Recipient generates a public meta-address (spending key + viewing key) | Recipient |
| 2. Create | Sender uses the meta-address to derive a fresh one-time stealth address | Sender |
| 3. Publish | Sender publishes an announcement so recipient can find their payment | Sender |
| 4. Scan | Recipient scans announcements with their private viewing key | Recipient |
What We Built — Three Layers
Intro Layer
The idea: Private one-time receiving addresses that break the link between sender and recipient.
Product Layer
The app: A full frontend for key generation, stealth payment creation, publishing, and scanning — try it live.
Tech Layer
The crypto: ML-KEM-768 (post-quantum) + view tags for fast filtering + announcement registry.
Under the Hood — For the Curious
What is ML-KEM-768?
What is ML-KEM-768?
ML-KEM-768 is a NIST-standardized post-quantum key encapsulation mechanism (FIPS 203). It lets two parties establish a shared secret even if an attacker has a quantum computer. SPECTER uses the
ml-kem crate for all encapsulation and decapsulation operations.- Public key size: 1184 bytes
- Ciphertext size: 1088 bytes
- Shared secret: 32 bytes
What are view tags?
What are view tags?
How does the announcement registry work?
How does the announcement registry work?
When a sender creates a stealth payment, they publish an announcement containing the ephemeral ciphertext and view tag. The recipient periodically scans these announcements using their viewing secret key. The registry can be in-memory (for testing) or file-based (for persistence).
What chains does SPECTER support?
What chains does SPECTER support?
Currently, SPECTER supports Ethereum and Sui chains. It uses ENS for Ethereum name resolution and SuiNS for Sui name resolution. The core cryptography is chain-agnostic — only the name resolution and on-chain settlement differ.
Technical Flow — How the Crypto Maps
What’s Next?
Explore the Product
Take a visual tour of the hosted app and see every step in action.
Integration Quickstart
Run the full keygen → create → publish → scan loop with copy-paste commands.
Core Concepts
Dive deeper into architecture, protocol flow, and cryptography.
FAQ
Get answers to common beginner and integration questions.
You don’t need to understand the cryptography to use SPECTER. Start with the product tour, then integrate — the crypto details are always here when you’re ready.